Latest News
Latest blogs and updates from SonicWall-Sales.com
Online attacks continue to grow
Unfortunately, and apologies for being the bearers of bad news, but online attacks aren't going away anytime soon. In fact, they're growing! Growing in sophistication and targeting, bypassing weaker security systems and hence having the power to evolve.
Cyber threat reports, like the ones carried out by SonicWall online, have recently shown a staggeringly high increase in ransomware attacks in particular.

Reports show that in the first six months of 2018, 5.99 billion malware attacks were carried out, equating to a whopping 102% increase compared to the same six months in 2017.
Two big-named threats
Ransomware such as WannaCrypt (also known as WannaCry) and variances of this malicious software have added to this increase with this particular ransomware first striking systems in 2017 and playing havoc with networks ever since.
The basis of this ransomware is where the malware encrypts user data and then hides it for ransom until the victim pays.
Unfortunately, threats like this are very real and especially linked with the encryption of data“ - nothing can be considered safe any more.
To help stop such attacks from getting through operating systems in the first place, people can set up firewall devices, and SonicWall security to block access to certain parts of the Internet. Your firewall should act as your first line of defence in setting up any networks and new devices.
One of the biggest online security threats has been the emergence of the Meltdown and Spectre vulnerabilities, which have affected multiple CPU vendors.
Meltdown and Spectre vulnerabilities ultimately allowed side-channel attacks that abused operating systems' memory to steal user information and confidential files.
SonicWall Real Time Deep Memory Inspection technology has been designed to protect businesses and individuals against these Spectre attacks. Looking at what these attacks are trying to achieve, how they access systems and stop these features from getting into your operating systems, and providing the highest level of security in a device.
Changing with the times
Online attacks, like everything, change with the times. They follow the latest trends and where people are spending or using money, and these attackers jump on the bandwagon.
An example of this has been the rise in stealing cryptocurrencies. Using stolen information as leverage or hacking into operating systems to build upon this growing trend.
At SonicWall we monitor trends, and we ensure that the SonicWall firewalls also stand up against any new and unusual threats, offering you complete peace of mind that you don't need a new firewall device every time a new threat is introduced.
It's also important to be aware that there has been a rise in fake ransomware attacks, where demand is made, but no files are encrypted or any data etc. stolen and used.
Fake ransomware means just that; they’re fake. However, because not everyone is aware what is fake and what is not and things to look out for to spot a fraud (check out our posts and guides on how to spot a fake), we often don't realise that if you are a victim of fake ransomware, then your files can be restored. But there is a little bit, because most users will probably think their data is gone, i.e. that the fake ransomware has encrypted their systems, and they will have to reinstall everything.
Although all fake ransomware attacks have failed, the threat is still there, and in some cases, people can still damage their systems by doing a full reinstallation.
A different way
A note for organisations is that online threats are also now trying to find a different way in. What we mean by this is that they're now using non-standard ports as they are not necessarily thought to carry the same level of risk, as they may not have the same level of security.
However, over 19% of malware attacks last year came through non-standard ports. We advise all companies and their IT departments to apply the same level of care when using non-standard ports as they would with standard ports.
In 2018 attacks on IoT devices stood at 32.7 million and SonicWall security wants to play its part in bringing these extremely high figures down or at least stop attacks from happening in the first place.
Thousands of people buy SonicWall firewalls and security devices because of the trusted service they receive from our teams, the features and benefits they can provide, and the enhanced security they offer.
Call us today on 0333 2405667 to find out how you can stay protected online.
Related post: how to create a professional cold email without going to recepient's spam folder
SonicWall Firewalls take it to the next level
SonicWall Firewalls take it to the next level
Cyber-attacks are not only increasing every day, but they’re also growing in sophistication.
At SonicWall Sales we see these increases on public infrastructures, in the cloud, every day, posing numerous threats and costly fixes!

However, when it comes to offering security solutions for the cloud, there is still a lot of work to do.
Work in understanding its infrastructure, understanding how it works with the mobile era, and how we can zone in on these understandings to create the best security software available.
Why is this level of understanding important?
Well, IDC has recently reported that approximately 83% of projects are now virtual and a further 60% of bigger enterprises now use the cloud in some form.
In addition to these statistics, with continuous changes to the cloud, keeping projects and workloads secure has become more challenging than ever before.
But SonicWall firewalls are ready.
Continuously developing security software, SonicWall has recently extended security to the public cloud (enhancing and taking it one step further from the private cloud), providing start to finish security for multiple cloud deployments - all through the SonicWall Network Security virtual (NSv) firewall series.
The benefits of cloud technology are widely known, offering users scalability, greater flexibility and agility, infrastructure consistency and improved business efficiency. And now, with SonicWall NSv, Microsoft Azure and AWS (Amazon Web Services) are to be included in the public cloud environments.
An industry-leading firewall series
The SonicWall NSv series offers users:
- Application control and intelligence
- Monitoring in real-time
- IPS
- Inspection and decryption
- Advanced cyber-attack protection
- Network segmentation and VPN capabilities
All designed and developed to protect Azure and AWS environments.
The NSv is the next generation to the SonicWall hardware firewall, which includes the features that customers like and admire most. Such as the innovative technology - Reassembly-Free Deep Packet Inspection (which is patented), and the Capture Advanced Threat Protection sandbox which provided real-time. Deep Memory Inspection, both designed to stop cyber threats and attacks in their tracks.
If you’re looking to control traffic and get complete transparency across all of your virtual networks and private clouds, then NSv is for you. Providing you with seamless security, enhanced management capabilities, increased performance, reduced operating costs, a drive in innovation, quick placement, and more - NSv makes a move to the cloud safer and more straightforward.
Solutions to cloud security needs
Cloud security is of the utmost importance, and NSv in all of its many models is on hand to address the issues surrounding public cloud data and applications.
Benefits to protecting your public resources and cloud infrastructure include gaining clarity into the virtual world of threat prevention, you can implement security zoning and appropriate policies, and you can be in a stronger position to protect against everyday hackers and threats.
You can also stop service disruptions from happening and maintain the highest levels of security, remaining compliant and risk-free, all without having a negative impact on performance.
SonicWall firewall VPN can be used in VPN deployment, secure connectivity, as well as used to tighten remote access and more.
Make SonicWall NSv THE security choice when it comes to the public cloud.
With patented technologies, the best in the business technological innovation to support the latest developments, and powerful security now extending to the
public cloud, for the best security systems in the market, SonicWall provide it with all.
Note: The date for AWS availability is pending; however, SonicWall NSv is available for Azure public cloud environments now.
At SonicWall Sales, we provide the latest in security software and hardware systems, and we’re always on hand to answer your questions.
Call us today on 0330 1340 230 to find out more.
SonicWall firewalls support SD-WAN (Software Defined WAN)
The software-defined wide area network (SD-WAN) is a specific application of software-defined networking (SDN) technology applied to WAN connections, which are used to connect enterprise networks – including branch offices and data centers – over large geographic distances.
A WAN might be used, for example, to connect branch offices to a central corporate network, or to connect data centers separated by distance. In the past, these WAN connections often used technology that required special proprietary hardware. The SD-WAN movement seeks to move more of the network control is moved into the “cloud,†using a software approach.

SD-WAN technology allows organizations and enterprises with branch locations to build highly available and higher-performance WANs. By using low-cost internet access (broadband, 3G/4G/LTE, fiber), organizations can cost-effectively replace expensive WAN connection technologies such as MPLS with SD-WAN. SonicWall delivers comprehensive, industry-leading security solutions that simplify SD-WAN deployments.
SonicWall Capture Security Center (CSC) Features
What are the feature differences between CSC/Cloud GMS tiers?
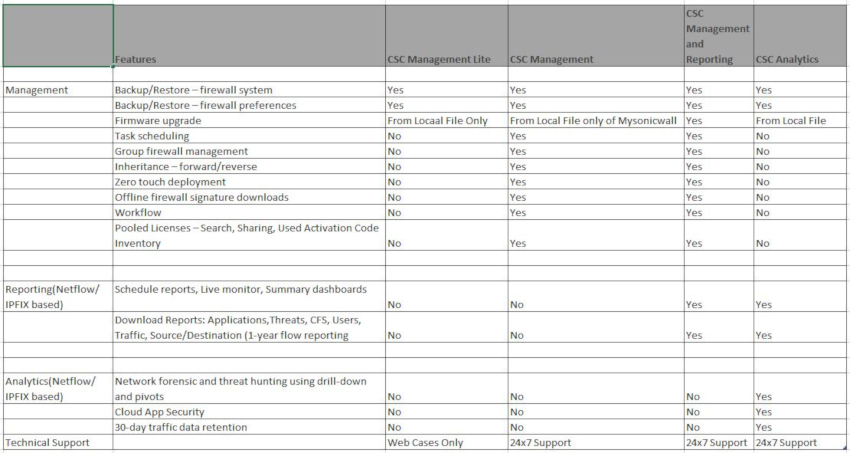
Full details at https://www.sonicwall.com/support/knowledge-base/171018140338183/
How firewalls work against threats?
You likely have seen your computer display a message about your firewall. You know it keeps your computer safe, but what do firewalls do to protect you?

How do firewalls work?
Firewalls are software programs that prevent someone from accessing your computer. It identifies inbound threats and isolates them so that they don’t have a chance to wreak havoc with your system.
They’re not just good at keeping viruses, malware, and so on out, though. They can also be used to prevent the transmission of sensitive data out of your system. So, if you have an employee who is trying to transmit protected files, the firewall can prevent that.
Finally, a firewall might also be programmed to block what it deems malicious sites or sites that are considered a no-no. If you’re running a business and would prefer that your staff do not access social media while at work, the software can be programmed to block access to those sites.
Essentially, a firewall works by following a set of parameters that your IT professional puts in place. If it comes across a request, incoming or outgoing, that falls outside of those parameters, it will block that request.
By blocking any requests that do not fit the preset parameters, it ensures that your entire system is safe.
About SonicWall Firewall
There are different firewall types out there. Some are relatively simple and focus on just keeping malware off your system. Others, like those provided by SonicWall firewall, can do much more. It is one of the reasons that many businesses choose SonicWall firewall for internet security.
These firewalls have become an integral part of our business community here in the United Kingdom and worldwide. The proprietary SonicOS operating system used to power every SonicWall firewall appliance offers reliable performance every time.
Getting your device is simple enough. You only need to contact SonicWall Sales. They’ll work with you to find the right option for your business.
You’ll have to choose between the SonicOS basic operating system and the SonicOS Enhanced operating system. Newer devices will come with the Enhanced operating system. The primary difference between the two is that the Enhanced version provides:
- Zone Management
- WAN load balancing
- ISP failover services
SonicWall set out to provide a service that would crush the others on the market. They wanted it to be the best available and to provide an alternative to services that didn’t quite make the grade. As their existing clients can attest, they were more successful than anyone could have dreamed.
Why choose SonicWall?
If you take your enterprise security seriously, this is the best option for you. SonicWall is highly effective at not only blocking threats but also identifying potential risks. You’ll get the level of protection that you need, at a cost that is reasonable.
Maybe you want a program that can identify and ward off malicious programs. Maybe you need the added protection of having incoming emails thoroughly vetted before they hit your servers. Perhaps you want to be able to have complete control over what sites your staff can access.
No matter what level of protection you are looking for, this company has the right option for your needs. They have built their reputation as being:
- One of the top cybersecurity companies worldwide
- An innovative company, always looking for new approaches to make systems even more secure
- The industry expert when it comes to cybersecurity
- A provider of products that work reliably and that will not let you down
- Very in tune with their clients’ needs and always willing to improve their product offering
Many companies say that they produce the best products on the market. In the case of SonicWall Sales, this is not an idle boast.
If you want the best of the best in cybersecurity, there is only one choice – SonicWall Sale
Why a business VPN is more important than ever in 2018

Whether you are running your business through the office or any other secret place, VPN for business is more important in 2018 than any year ever. In this highly competitive world, Virtual Private Network has become a need rather than just an option.
Recently, there have been a lot of cyber attacks observed in most of the countries that forced authorities to make drastic changes in their privacy laws. This is also one of the reasons why VPN has become a necessity for individuals as well as big businesses. No matter what type of business you are running, you need to have a digital presence and this is a reason why business VPN for 2018 is in such a high focus.
In last few years, the attack from Ransomware has shaken the entire world and businesses are taking every single step to keep their data secure and safe. It is a kind of malware that secretly encrypts your data and use it as a hostage to demand any amount of money which needs to be credited to some anonymous account. The last couple of years have witnessed many cases where corporate were requested huge ransom in return for their crucial files and data. It is estimated that cybercriminals have made more than $1 billion through this illegal means. In the year 2018, businesses have started realising the importance of VPN that improves the security of your network and lowers any risk of data being encrypted or stolen.
Social networking is another platform where private information of users is being compromised and sold to the agents or advertisers which they can use to know the buying behaviour of people. Today, users are becoming conscious about their information and they are not ready to accept any breach of their private data. Virtual Private Network provides an ideal platform for all the internet users to protect their crucial data such as search results and online shopping patterns. 2018 is the year when internet users have started using advanced security methods such as VPN that allowed them to browse social networking sites without any fear of data breach.
In last few years, cryptocurrencies such as Bitcoin have shown much volatility in the prices and it attracted many new players to enter this market to earn some hefty returns in short period. However, just like other industries, cryptocurrency sector was also witnessed many attacks from cybercriminals who transferred bitcoins from the bitcoin wallet of several account holders. This is an aspect where VPN is very useful as it helps to protect the network of a user so there will be no leakage of username or account's password. Most of the key players in the cryptocurrencies are focusing on adding VPN as an inbuilt feature in their software to offer an additional level of security to account holders.
As the number of users taking help of internet to do their everyday activity is increasing every day, the demand for security solutions such as VPN will keep rising in coming time. Here at SonicWall-Sales, we offer the best VPN deals in the UK.
Comparison of business firewall VPN Services
 Virtual Private Network plays a vital role in developing an encrypted and secure connection to a less secure network such as the internet. VPN offers encrypted tunnels which look after network traffic and maintains the confidentiality of communications. It is mostly used to provide secure access to end-user devices that mainly include laptops, tablets, Smartphone and personal computers. There are several service providers available in the market that offer the functionality of VPN. Go through following points to check out the comparison of business firewall VPN services:
Virtual Private Network plays a vital role in developing an encrypted and secure connection to a less secure network such as the internet. VPN offers encrypted tunnels which look after network traffic and maintains the confidentiality of communications. It is mostly used to provide secure access to end-user devices that mainly include laptops, tablets, Smartphone and personal computers. There are several service providers available in the market that offer the functionality of VPN. Go through following points to check out the comparison of business firewall VPN services:
- Cisco VPN solutions:
The VPN service of Cisco is based on wide range of products such as AnyConnect. It is a product based software which can be run on all mobile OS and desktops. Cisco VPN solution does an outstanding job in performance metrics. Apart from VPN termination, it also offers some other functionality.
- Dell SonicWALL VPN services:
After acquiring SonicWall, a giant technology company Dell started providing a wide range of appliances which are mainly dedicated to remote and secure access. The first is the SRA appliance that mostly emphasis on SMB environments and it is quite restricted to the VPN concentrators. On the other hand, E-Class SRA appliances cover much additional functionality such as malware protection and mobility management. This is a key reason why Sonicwall VPN service for business and Sonicwall VPN for enterprise solution are in such high demand.
SRA appliances are classified into three different categories which are SRA virtual, SRA 4600 and SRA 1600 appliance.
- F5 Networks VPN services:
F5 Networks VPN solution used to be served as a comprehensive suite and standalone product. IT includes VPN functionality in the form of APM. It helps a wide range of functionality that involves a knack to connect via the deployed appliance. This functionality is provided for almost every mobile platform and desktop computer. The level of performance mainly depends upon the common platform on which module is deployed.
- Citrix VPN services:
The VPN access solution of Citrix is merged into NetScaler Gateway which offers an easy way for customisation. NetScaler Gateway provides more than just VPN functionality. It provides secure access to XenMobile, XenApp and XenDesktop sessions. Considering the traffic status, the support for DTLS and TLS sessions is provided by Citrix Gateway. It is also added in NetScaler ADC appliance and combined into the different Citrix applications. You can consider deploying it as a part of appliance solution or virtual device.
Each of the VPN solution discussed above comes with different appliance alternatives that feature unique specification. So remember to go through all the specification details such as how many users will be secured and how many concurrent sessions will be available. Once you have selected the right option, you are good to go.
The licensing structure of all above firewall VPN services mentioned above is quite complex and it mainly depends upon the platform which has been deployed. So before making any decision to choose VPN solution for your business, make sure you seek valuable inputs from an expert in the field.
What is VPN and why does my business need one?

Virtual Private Network plays an important role to bring in advanced security to your network using highly advanced security methods. VPN looks after your data safety when you use any public network to transfer data from one device to other. VPN is extremely handy when it is practically unviable to use any unique device to protect your network. When we talk about VPN for business security, it definitely has a crucial role to play in its varied range of applications:
- VPN service lets your employees execute their job from any location of their choice. By offering remote access to your staff, you can increase their productivity and efficiency which will ultimately bring a lot of positive results for your business.
- What VPN does that it provides you with a temporary IP address and hides your primary IP address. This way there will be a low risk of data loss and you can easily share any form of sensitive information with your staff.
- Once you start using VPN in your system, you will experience a significant boost in the performance of your operations. This is mainly because of fast data transmission without any lag in the speed and performance.
- From the business point of view, VPN is more economical than any other form of private network. Instead of hiring distance networks to facilitate safe data transfer, businesses can utilise their current public network using Virtual Private Networks.
- If you are planning to set up Virtual Private Network in your system, then you need to consider the scalability factor as well. Businesses need to consider growth aspect that may result in an increase of infrastructure and employees. In case of expansion, it will be quite expensive to replace entire VPN setup with the new one. Thus, you need to consider the growth factor while installing VPN for your business for the initial time.
- Most of the time, the performance of VPN is not entirely under your control and you need to depend on your internet service provider to achieve a particular level of performance. So make sure you get in touch with your internet provider and discuss all your requirements with him.
- VPN makes it possible for you to hide the identity of any user in your network by giving him an anonymous status. This way you can protect the client's data from other users available on the network. You can also rely on data safety methods like encryption that makes it impossible for hackers to track any data that is being transmitted in your network.
At times, VPNs can be bit complex to configure and install in your system. So make sure the person who is looking after the entire VPN set up have proper knowledge of issues related to your network security. Though Virtual Private Network (VPN) brings many advantages for your business security, it also comes with few limitations. To identify all these limitations and try to fill the loopholes involved in the system by taking some vital steps. To browse our available VPN’s, click here.
What is involved in setting up a SonicWall VPN?

When you talk about protecting a system from hackers, viruses and other threats, the first thing that comes to mind is a firewall. SonicWall is one of the most famous companies when it comes to firewalls. It is one of the known companies working towards preventing cyber crime for more than 25 years. They have served more than 500,000 businesses spread across 150 countries through their innovation, products and partnerships. One of their most popular products is the SonicWall VPN. This VPN gives users secure access to applications and files at remote locations. If you are new to SonicWall VPN, you will surely have some questions regarding its setup.
Well, setting up a SonicWall VPN is not complicated. You simply need to follow a series of steps and it is done.
- Before you start the VPN setup, you need to configure the Sonic VPN device. For configuring, you need to log in to the device and click on the VPN button. Follow the steps mentioned by VPN Policy Wizard and complete the setup.
- There are two options to set VPN – site-to-site VPN and WAN GroupVPN.
- Now, on the master unit, go to VPN option and then look for Settings. Under this tab, tick the Enable VPN option. To make it easier, change the name of Unique Firewall Identifier to an easy to remember a name. Once you have entered the new name, click on Accept.
- You also need to add details in other fields in the form of authentication type, IKE Authentication and more.
- Next click on the Network tab. Here the setting will change depending on whether you are on the local network or remote. For a Local network, look for the LAN Subnets options present in the drop-down. For remote access, you need to create a new Address Object.
- After Network, you need to fill the Proposals and Advanced tabs. Ensure that you add information to all the fields. Once done, click on OK button.
- To review your VPN policy, see the VPN Policies page.
- Every SonicWall VPN has two devices – a master and a secondary device. Now repeat the same steps on the secondary devices – a master and a secondary device.
- The proposal on Master device should match the other device.
- Make sure you tick the Enable Keep-Alive option in the Advanced tab.
- Once done, click OK to save the policy on the other device also.
- You can always make changes to the VPN policies to control what traffic is allowed to follow through the tunnel. To expand access, you need to create additional Address Objects on each of the firewalls.
While configuring SonicWall VPN, you need to ensure there are no typing errors or problems in the WAN connections. You need to check that the network that you refer to as local on one side need to be referred to as Remote on the other side and vice versa.
Site-to-site VPN connections with SonicWall is fast and easy! It can be done in many ways, so choose a method that suits you.
Read next article: how to create a professional cold email without going to recepient's spam folder
Applying for SSL Certificates using Sonicwall VPN Connections
ith a Sonicwall SSL virtual private network (VPN), it is possible for you to use VPN solutions that make it possible for you to access corporate assets remotely through broadband in a dependable and safe manner. When a network administrator wants to install a certificate to enable the device to be accessed with a certificate error, they will need to request for the certificate and import it from its authority. In order to do that, you will need to create a request for certificate signing using your appliance. Here is a detailed guide to use when applying for certificates for SonicWall firewall connections.

Steps to Apply for A Sonicwall VPN Connections Certificate
- First, you will need to log into your appliance. You can then click on System>Certificate>New Signing request
- Fill Fully Qualified Domain Name (FQDN) that you intend to use for SSL and fill out the Certificate Signing Request.
- You can now download CSR. Use the text editor to make any edits. One of the best options that you can use is Notepad++. This is because it keeps a format that will make it easy to copy the CSR request over to the Certificate authority.
- Contact the certificate authority and ask them for the SSL. Provide the CSR when they request for it. Take note that when you are downloading the already signed certificate from a Certificate Authority like Thawte or GoDaddy, you will need to choose a server platform such as Apache SSL.
- Once the Certificate Authority has been given a certificate, you will need to upload it to Pending Request.
Installing the SSL Certificate
- The Certificate Authority (CA) will send the SSL certificate via email and will be included in a zip file. All you will need to do is to download that zip file before extracting it to the server directory. You can then create a fresh zip file using the name certkey.zip. These two files should be inserted in “server.ley†or “server.crt†into the specific folder.
- A pop-up window will appear. Click on the button marked “Browse†and choose a server.zip file to get into your email. Then click on the “Upload†button. This will bring up the certificate on the list of certificates under the certificate page.
Setting up the SSL certificate
- Click on System > Certificate page > Server certificate. This is usually at the right side of the SSL certificate, showing pending request. Then click on the icon dubbed Configuration.
- You will be required to input the password that you created during the CSR generation.
- You should then click Submit.
Making Changes
- You will once again need to click on System > Certificate page > Server Certificates. Now you need to choose the certificate that you would like to make active.
- On the page of System > Certificate page, you will need to click on the button marked Apply.
- You should then restart your appliance
- In order to restart it, you should expand the table under System>Certificates>Restart
With these steps, you would have completed the installation of your SSL certificate.
Acquiring Certificate for Sonicwall VPN Connection
It is usually considered to be more secure to use digital certificates for the purposes of authentication rather than using the VPNs pre-shared keys. One of the methods that are commonly used to authenticate 2 peer devices while establishing an IPsec VPN tunnel is through the digital certificate. Another option is through IKE that uses pre-shared keys. Some of the features that come with IKE authentication that is certificated in the SonicWall VPN connection includes:
- A digital certificate that is provided by a third party CA such as Verisign.
- The administrator at SonicWall can create a CSR and have this signed by the CA.
- There is a need for the two parties to trust the certificate’s issuer.
This article will guide you on acquiring certificates the from Sonicwall VPN connection. This certificate signing process that we are guiding you through uses the Windows Server 2008 CA.
Creating A Certificate Signing Request
- You will need to start by logging into SonicWall’s management GUI.
- Click on System and then Certificate page.
- Navigate to New Signing Request in order to create the same CSR
- Click Generate in order to save
- Refresh that page
- Click download
How to Get A Certificate For The Wan Groupvpn Configuration
- On your browser, you will need to go to the enrollment page on Microsoft Windows. You can find it on http:///CertSrv
- You will be prompted to authenticate. You will need to enter your username as well as the password.
- You can now go to Request a certificate > Advanced certificate request
- Use the Saved Request box to copy the CSR’s content.
- Click on Certificate Template and choose Administrator. You should take note that the web server or user template can also end up chosen.
- You can enter san:email=<local-part@domain.com or san:dns=yourdomainname.com. After clicking Submit, you will go to the next page where you can now click on Download Certificate. This will make it possible for you to save the already signed certificate to the disk.
Downloading CA Certificate
- Visit the enrolment page of Microsoft Windows on http:///CertSrv
- Click on Download CA certificate
- Move to the next page and again click Download CA certificate. You can save in on your disk
You can visit SonicWall VPN connection and use the button under CSR pending request to upload the already signed certificate. In order to gain trust and to validate the already signed certificate, you can import it.
Getting Certificate for The GVC Clients
- You will need to go to http:///CertSrv. This is the certificate enrollment page for Microsoft Windows.
- You will be asked to authenticate details. You will need to enter your username as well as password of the domain user
- You can request the certificate
- Click under the advanced certificate request
- Go to certificate template and choose User or Administrator
You should bear in mind that if you need a site to site GVC or VPN that has Key Usage, where present, you should have digital Signature as well as Non-Repudiation and an Extended key Usage (EKU). Where this is present, there is a need for Client Authentication, if it works. If you are using L2PT or IPSec VPN and there is Key Usage, ensure that you make use of Digital Signature or/and Non-repudiation.
Importance of Sonicwall Training and Certification
At SonicWall University, you will get access to sophisticated online courses that are designed to provide you with certifications that are up-to-date. Once you join the courses, you will have access to a wide range of e-learning certification modules, certification examples and authorised training partners.

The SonicWall training programs are suitable for network administrators and security experts who are aiming to improve their knowledge as well as increase the investment they have made in the SonicWall network Security Products and applications. With the NSAA (Network Security Advanced Administration), it becomes possible for students to configure, optimise, monitor and manage firewall appliances that run using SonicOS.
Trainings Offered by Sonicwall
The SonicWall training makes it possible for system administrators to deal with many evolving network challenges and threats to the cybersecurity space. Some of the courses leading to SonicWall certification include:
- Network Security Advanced Administration (NSAA). This is a training that makes it possible for system administrators to deal with many evolving network challenges and threats to the cybersecurity space. This is a course that is recommended for system administrators and networking professionals that are involved in the day to day operation of security gadgets. After completing this course, the graduate will be in a better position to configure SonicWall firewalls to ensure a Secure as well as Remote connectivity. This is on top of preventing advanced threats and Network Optimization. After completing the NSAA course, you become eligible to enrol for the CSPP (Certified SonicWall Security Professional) exam. One of the SonicWall training essentials is to have completed the (SNSA) certification or at least the legacy CSSA. In order to sit for the CSSP exam, you need to have successfully completed the CSSA or the SNSA after a period of 2 years study.
- SNSA. This is a course that is recommended for the networking professionals whose role is to handle the day to day operation of different security gadgets. The course was created to help students understand technology in network security that is SonicWall-specific. This course has been built to serve the SonicOS .65 firmware that was recently released. It consists of only 20% classroom lecture and 80% hands-on training in the labs. This is an upgrade from the NSBA which has been retired.
- CSPP. This is a more advanced course that is the right choice for individuals that optimise, deploy and troubleshoot all the features of a product.
Conclusion
The Network Security Basic Administration(NSBA) was based on the right understanding of different security issues with a bias against the administration. The goal of the training was mostly to train network security administrators. However, it was noted that students did not get in-depth training on the Sonicwall firewall, but the training emphasised on giving a general overview of network security.
The new SNSA has now been designed to fill this gap. Its goal is to teach students network security technology that is SonicWall specific, and the skills necessary for the implementation and the configuration of firewall appliances. Therefore, there are some good reasons for enrolling in SonicWall training and certification.


