Latest News
Latest blogs and updates from SonicWall-Sales.com
‘3 & Free’ Promotion: How to Upgrade Your SonicWall Firewall for Free
What is the SonicWall ‘3 & Free’ Promotion?
The limited-time SonicWall ‘3 & Free’ promotion is the easy, cost-effective way for customers to upgrade to the very latest SonicWall next-generation firewall appliance for free.
Through Oct. 31, 2020, eligible customers may receive a complimentary NSa 2650, TZ350 or SOHO 250 appliance by purchasing a bundle that includes a three-year subscription of the SonicWall Advanced Gateway Security Suite from their authorized SonicWall SecureFirst partner.
This security suite includes everything you need to stay protected against today’s modern attacks, including advanced malware, ransomware, encrypted threats, viruses, spyware, zero-day exploits and more. This complete service includes:
- Capture Advanced Threat Protection (ATP) sandbox
- Gateway Anti-Virus and Anti-Spyware
- Intrusion Prevention Service
- Application Control
- Content Filtering Service
- 24×7 Support
SonicWall’s exclusive security subscription service also includes SonicWall Real-Time Deep Memory Inspection (RTDMI). A patent-pending technology, RTDMI™ enables Capture ATP to detect and block malware that does not exhibit any malicious behavior or hides weaponry via encryption. This protects your organization from zero-day attacks, malicious PDFs and Microsoft Office files.
How to configure SSL VPN on SonicWall
SSL VPN license ultimately allows users who are working or operating remotely to connect to internal networks and resources safely and securely through the SonicWall.
Setup of SSL VPN is through the software solutions; SonicWall SSL VPN client, NetExtender, and the SonicWall mobile connect client.

Configuring SSL VPN on the 7.X SonicOS
For the address ranges within SSL VPN IP v4, you first need to create your address object.
An administrator will need to log in to your UI firewall management and choose object from the menu.
Look for match objects and addresses, and then click add.
A second window will appear where you can then include the identified range for SSL VPN.
You then need to configure the SSL VPN by navigating to within the server settings to network SSL VPN and opting for SSL VPN status on zones.
From here, you can change SSL VPN access by switching to enable or disable (note, green indicates an active status).
Within the SSL VPN server settings, you then have the option to select domain and SSL VPN port.
(Note: the port option will be required if you connect using the NetExtender and mobile connect methods. The domain will be necessary for the user to gain access to the networks and log in.)
From the client settings – SSL VPN Network, choose default device profile and set the SSL VPN for zone IP v4 and set the address object generated previously as the Network address IP v4.
The tab across the top of the window labelled client routes allows you to manage what levels of network access remote users can be permitted via their connection.
The last tab, client settings, allows administrators to input suffix, WINS, and DNS information and control the caching passwords, behaviour of NetExtender clients, and usernames.
Change create client connection profile to enable and save all changes.
Adding additional SSL VPN users
NetExtender users can authenticate SonicWall for local users, or if they’re listed within a known group, this can be done through LDAP.
To add local users, you need to be within local users and groups, which can be found within devices and users. You can now add new users by simply clicking add.
Moving to the tab labelled groups, click SSL VPN services, and move this across to member of, section.
Moving across to VPN access, you can now add all relevant areas that the user will need access to.
Again, make sure to click save before closing the window.
For the zones of SSL VPN, it’s important to check access rule information.
To do this you need to access, access rules by following policy – rules and policies, then choose SSL VPN – LAN rules. If a user requires access to other zones to obtain resources, this can all be managed in this area by verifying and adding additional access rules as you go.
Configuring SSL VPN for the 6.5 SonicOS
Similar to the SonicOS 7.x, administrators will need to log in to the management platform of SonicWall and within the navigation menu choose manage and then address objects.
From here, click add.
A second window will appear where you now have the option to add your range for SSL VPN.
To configure these settings, click on SSL VPN on the settings page and go to WAN, changing it from red to green to show it is now active.
Now all SSL VPN configurations will be enabled in this particular zone.
You can then set the domain and ports for SSL VPN as you require.
Move across to client settings where, as administrator, you can configure the range of client addresses and NetExtender settings.
For the default device profile, click on configure.
Here you can set the network address v4 IP as your address object from before and set the zone v4 IP as SSL VPN.
The tab labelled client routes will allow administrators to manage the level of access users have to two networks.
It’s essential to set the VPN appropriately as all users will be able to see the routes but may not necessarily be authorised to access all network resources.
In the settings, administrators should also enter all required DNS and WINS data and create client profile connections by enabling this action.
Adding additional users
To add new users, click on users and local users and groups. Within groups, click add SSL VPN services to move the field to member of.
Moving to VPN access, you can then add all the relevant IP addresses and objects identified to the users requirements, in terms of access via NetExtender.
Note: Client routes and VPN access must match for users to have authority to access network resources.
Remember to click save, to save all changes before closing.
SSL VPN zones access rule details
Within access rules, you can access SSL VPN LAN rules with drop-lists available.
Access rules allow access to intended end devices through SSL VPN IPs which are also required for the firewalls to understand that such traffic is allowed through.
You can also test all connections and configurations by installing the SonicWall NetExtender.
Two final points to note:
Remember, within the user’s section of the menu toolbar, you must add in however many users that will have login credentials. Each user then must become a member of SSL VPN services group and have to subnet added to VPN access within the allow list.
In-network interfaces make sure to click on configure on the WAN interface and tick the HTTPS box beside the user login – this helps to minimise login failed attempts occurring when users access SSL VPN via a web portal.
For further information on a SonicWall VPN licence and more call 0330 1340 230, today.
Read the next article: Best Practices for SSL VPNs
Setting up SSL VPN
SonicWall's security appliance features SSL VPN, providing secure remote access to networks using the NetExtender client.
Below, we outline the steps required to help configure the SonicWall SSL VPN setup, allowing you to run applications securely across your company's network.

Accessing NetExtender
Remote users will use NetExtender to access your networks and anything contained within these, i.e., documents, shared files, etc.
Typically users access NetExtender either by clicking on the NetExtender button found when logging in to the virtual office web portal or by launching the NetExtender as a standalone client (once installed, it will remain as a shortcut or within the Start menu making it easy to access after that).
How to setup SSL VPN for SonicOS 7.X
When setting up SonicWall SSL VPN on the latest 7.X firmware, the following instructions should help.
1. With the server settings, look for SSL VPN, Network.
2. Choose SSL VPN status on zones
3. You can choose whether you want and need to disable or enable access to SSL VPN (moving it to a green status means it is active).
4. You then need to move to the server SSL VPN settings. Here choose the port SSL VPN and the desired domain and configure within client settings SSL VPN, Network.
5. With the client settings, SSL VPN, you're able to configure the NetExtender client settings and the client address range information, i.e., which IP's you will provide for those connecting clients and where users can log in from.
6. For the default profile of the device, click on configure.
7. Change the Network IP v4 Address to the address range you inputted in point 5 and set the Zone IP V4 as SSL VPN.
8. Within client routes, you can now control network access for all users, deciding on what can and can't be accessed across the network.
9. The last tab, client settings, is where you can input Suffix, WINS, and DNS information, all while managing usernames, caching passwords, etc.
10. You must enable the create client profile connection for the NetExtender to make a connection and record the server name for the SSL VPN and domain name too.
11. To configure the SSL VPN virtual office's functionality and appearance, you need to use the SSL VPN portal settings page.
12. All SSL VPN users must be part of a user group or SSL VPN services member. To check this and change as appropriate within; device - users – local users and groups.
13. Moving across to VPN access at the top of the screen, you can choose one or more networks from the list, clicking the arrow button to move them directly across to the access list. If you need to change or remove a user's access rights, select the network from the access list and click on the arrow pointing left.
14. Finally, within policy, rules and access rules, set the SSL VPN to LAN rules. And if a user requires access to other zones, you can add and verify these via the access rules page.
SSL VPN setup for SonicOS 6.5
1. Select the SonicWall application and click on manage – SSL VPN settings.
2. To configure these client settings, you need to be on the SSL VPN client settings page where you can input the address range for the client, NetExtender information, and where the users will be able to log in.
3. Within the settings tab, make sure to select both network address IP V4 and Zone IP.
4. To allow the right level of access for users, administrators will need to set this within SSL VPN – client routes page.
5. To configure client settings for the NetExtender, the create client profile connection must be enabled.
6. For the virtual office portal's appearance and functionality, these elements must be configured within SSL VPN – portal settings.
7. Administrators will need to manage users and groups of users through users – local users and moving each member to the appropriate services group. When configuring local users, navigate to manage and system setup – local users and groups, you can then add SSL VPN services. To set local and LDAP user groups, you must edit SSL
VPN services and add the specified user group within the member's tab.
8. Within VPN access, you will see what users can access what networks. You can also add more networks to the access list as required. Of course, these can also be removed by carrying out the same procedure in reverse..
9. Note the new SSL VPN areas within firewall – access rules.
10. SSL VPN zones will auto-create firewall access rules; however, these can be modified, allowing access to only those users that have been configured.
11. Administrators should follow manage – network – interfaces, and within the WAN interface, administrators must ensure HTTPS is enabled.
Both of these SonicWall SSL VPN setup procedures can be tested via users through the SonicWall's public IP – always recommended.
Protecting your business during a global crisis
COVID19 has had a dramatic effect on the world. With companies changing the way they operate and work and teams are looking at different ways to communicate and access information.
A business’s focus during this time is on how they will continue to operate. And in all instances, people ultimately need access to the tools and information to help them get the job done.

To help keep businesses running and operating as smoothly as possible, we take a look at some of the best practices for businesses and why they're so important when protecting the business from a global health crisis.
A firewall approach to a global health crisis
During the Coronavirus pandemic, each country has taken its own approach to protect its people.
Countries like Japan have almost used the technological concept of firewalls and built their own manmade firewall around their cities. They were restricting travel, placing quarantine restrictions on areas, and limiting the volume of people coming in and out of the country.
Japan's focus was to create a firewall that blocked the Coronavirus's inflow, just like a firewall blocks malware accessing its networks and spreading.
However, as Japan found out, firewalls have to be robust, with no room for error or indeed holes in the system.
So, what can businesses of all shapes and sizes do to protect their online networks further?
Protecting business during the global crisis
1. Make sure you have a robust business continuity plan
Your business continuity plan is not just a nice to have; it's a must-have. It should be a plan covering everything from adverse weather conditions to cyber-attacks, global pandemics, and more! It's advisable that these plans are checked and played out (to some extent) annually and should account for all business areas, including infrastructure, technology, communication, etc.
2. Securely expand remote working
Remote working is not a new concept; however, having your entire workforce working remotely is unique! The problem that most businesses have come across when expanding their remote working capabilities is that they don't have enough VPN (a virtual private network) licences to accommodate everyone.
This can be a risky place to be in, not only because your employees no longer have access to information and applications needed to do their jobs, but you also run the risk of employees trying to access networks via non-secure connections.
The solution?
Businesses need to look at scalable, secure remote access solutions that can easily cope with an increase in users should the need ever arise.
3. Watch out for fear-based cyber attacks
Fear-based cyber campaigns are common among cybercriminals, and organisations must ensure that they have high or increased email security levels in place to help mitigate these cyber fear attacks.
Office 365 security, cloud application security, and endpoint protection solutions should all be implemented to prevent phishing attacks compromising networks.
4. Look after your endpoints
With more people working remotely, businesses must look at proactive endpoint protection that prevents attacks before, during, and after their execution.
Why cybersecurity matters now more than ever
We have an increased dependency on digital infrastructures. Today the internet and its many communication channels have become the only method (at times) for social/human interaction.
With more work from home policies coming into effect than ever before, workforces have been confined to social media posts, video calls, chat programmes, etc.
With this in mind, a cyberattack now, of any sort, on an organisation's network or across a family's devices would be devastating. Not only because of what the attack could cost you financially but because of what it can do to our mental well-being as all communication is lost.
Fear. As we've mentioned previously, cybercriminals are renowned for exploiting human weakness and thrive in the knowledge that people will, unfortunately, make more mistakes in times of global crisis. We need to be careful whom we trust with our data online.
For example, a recent cyber-attack occurred, which centred on a map that seemed to display Coronavirus statistics. However, Malware was concealed in this download, which then ran a malicious application on the computer and allowed hackers to access passwords and more.
Staying safe online
It's important to remember some best practice points when working from home or when looking at increasing your level of security online:
- Make sure you have a long, complex router password
- Check all firewalls are active on your router
- Don't reuse passwords across the internet
- Use only reliable VPN when accessing anything online
- Don't click links within emails that you're unsure of
- Be careful whom you give your details to
- Be sure to check the source of all URLs and ensure all apps and programmes you download are the original versions
- Update your system software and applications regularly.
Software for business protection
SonicWall-Sales firewalls help to provide the critical security business solutions that organisations need, now.
Also, providing remote connectivity, cloud application security, and endpoint protection, make sure to call the team to find out how SonicWall can help keep your business safe now and during a global crisis.
How your SonicWall Firewall can protect you against even the worst cyber attacks
Most people who are using some form of device connected online will have had, or fallen victim to a data breach, where their personal information has been compromised.
2020 has put the world in an uncompromising position as offices close and remote working and working from home becomes the norm.

Unfortunately, with this, there is also an increase in the risk of cyber-attacks and, most definitely, data security breaches.
Below, we take a look at those 2019 cyber-attacks that, while not the biggest, had the most considerable impact, and just what measures you can put in place to prevent them from happening again.
Cyber Attacks we must learn from
Fortnite
With the gaming sector bigger than Hollywood and the music industry combined, it fast became a high-profile cyber target. And in 2019, the popular game, Fortnite, suffered a large-scale cyber-attack.
Hackers took their opportunity when a vulnerability was found in the games login systems. At this stage, hackers were able to impersonate actual players, view game details, chats, and purchase currency, which could then be moved to their own accounts.
Of course, this issue was quickly rectified; however, the volume of people affected and impacted by the hack is huge.
Georgia Institute of Technology
Unfortunately, Georgia Tech found a vulnerability in its web application a little too late. It was reported that cybercriminals gained access to a personnel database containing 1.3 million individuals, both students, and staff, personal data.
Quest Diagnostics
An awful breach in 2019 that resulted in the loss of a considerable volume of medical data – Quest Diagnostics was identified as being the biggest single breach in this category, with 11.9 million patients affected.
The data stolen included patients' credit card details, medical information, and personal identity information – all adding to the cybercriminals armour ready for blackmail and identity theft purposes.
Toyota
Toyota faced a serious hacking attack in April 2019, when 3.1 million customers and employees had their personal information stolen. Names, birth dates, and more were all taken when hackers gained access to Toyota's internal computer systems.
How could we forget about Facebook with all of the daily media reports! As a social networking platform, Facebook is constantly under review, and when not one, but two breaches related to privacy were detected in 2019, we fast saw Facebook users (approx. 2 million) have their personal information exposed.
The silver lining is that these particular vulnerabilities weren't uncovered by cybercriminals but rather researchers looking for security flaws.
First American
First American experienced a big blunder when they found out in April that 885 million customer records were available on their website for simply anyone to steal. With information dating back to 2003, records included customer's social security numbers, driving licence details, financial data, and more!
Magecart
A malware attack that was widely distributed throughout 2019, Magecart affected an estimated 18,000 web hosts! This piece of malware hijacked the online cart systems that people use when making an online purchase—stealing people's financial details throughout the process.
Choice Hotels
Choice Hotels fell victim to ransomware back in August 2019 when approximately 700,000 customer records were accessed. A ransom note placed over the server demanded Choice to pay in Bitcoins for the stolen data's safe return.
Canva
Australian company Canva was targeted in May by cybercriminals who claimed they had accessed over 139 million users' details, which they were planning on selling on the dark web!
Taking Action
The failure to patch a known vulnerability, in a timely fashion, can have severe consequences. Not only this, but unsecured databases that are left exposed online are also a significant problem.
Learning from our experiences, we understand that data breaches and cyber-attacks can come in various forms.
We also know that, unfortunately, cyber-attacks aren't going anywhere fast, which means for businesses and individuals, we need to look to increase and take charge of our cybersecurity now.
Ideally, taking a layered and robust approach to cybersecurity is required today, as is real-time cyber-attack detection and robust prevention platforms, like the
SonicWall Firewall systems.
Best practice for tackling cybercrime includes:
- Scaling your cybersecurity throughout all networks (wired, wireless, and mobile).
- Using firewalls to fight against advanced cyberattacks.
- Put in place cybersecurity layering measures with sandboxing, ideally opting for SonicWall Security.
- Implement robust email controls to prevent phishing attempts.
- Plan your network data.
And most importantly…
- Assess your business's cyber strategy and the landscape that you operate in – continuously.
According to research by IBM, the cost of an average data breach can be up to $3.92 million with FireEye reporting that just under half of all businesses are prepared to face a cyber-attack or data breach.
SonicExpress Mobile Application
TZ570 and TZ670 Series firewall customers now have a new way to ease and enhance their onboarding experience.
For most of us, mobile devices are becoming the go-to means for getting work done in a digitally connected world. By 2023, the number of mobile device users will increase to 7.33 billion — and by 2025, 72% of those accessing applications and the web will do so with smartphones alone.
Network admins are also utilizing mobile devices to get work done: These devices allow them to extend their presence, enabling faster responses and easier network configuration and setup.
As part of our commitment to anytime, anywhere cybersecurity, SonicWall is launching the SonicExpress mobile app. The SonicExpress mobile app greatly simplifies firewall onboarding: device registration, initial setup, basic configuration, and monitoring for 7th generation SonicWall firewalls, including the recently launched TZ670 and TZ570 series. Designed for the Apple and Android platforms, the SonicExpress app is now available for download from the Apple App Store and the Google Play Store.
Onboarding as easy as 1, 2, 3
The typical onboarding process involves appliance registration and several other steps that must be completed in order to get a new firewall ready for configuration and use. With SonicExpress, the onboarding experience of a new firewall involves just three simple steps:
- Launch the SonicExpress App on a mobile device
- Connect a mobile device USB cable to the new firewall
- Finish setup
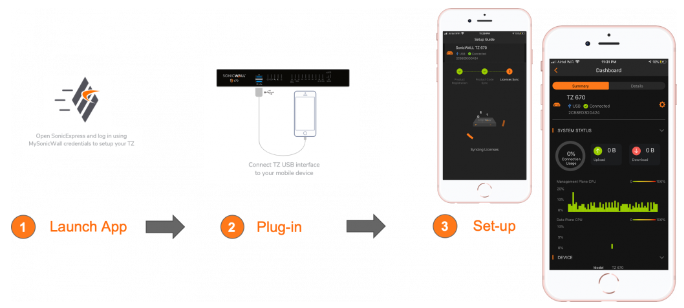
Designed with intuitive interfaces, the SonicExpress app guides the user through device registration and initial setup in less than a minute.
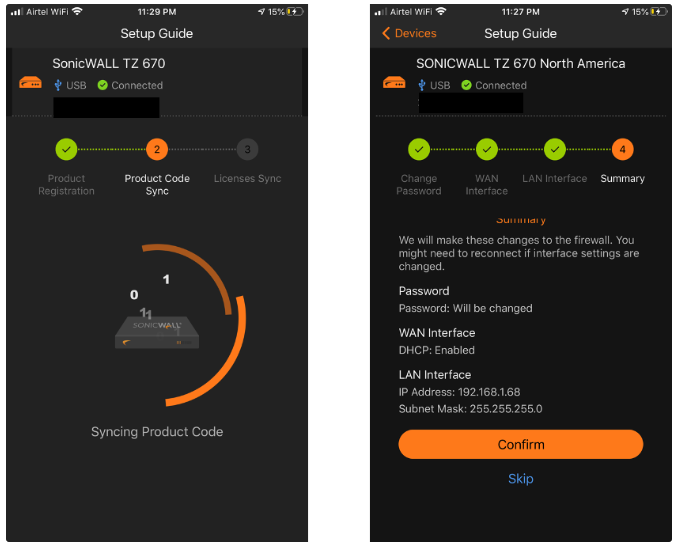
Simplified initial firewall setup
Zero-touch deployments require firewalls to connect to the internet using a DHCP address on the WAN interface. However, in certain deployments, WAN interfaces are assigned static IP addresses or configured over a PPPoE interface. For closed network deployments, there is typically no internet connectivity for the firewall being set up. The app helps with these and other initial setup configurations by connecting the firewall using the USB interface.
The SonicWall Express Setup Guide walks users through the process of getting their firewall registered and set up for specific deployment use cases. Alternately, users can choose to register the firewall without going through the entire setup process by simply scanning a QR code.
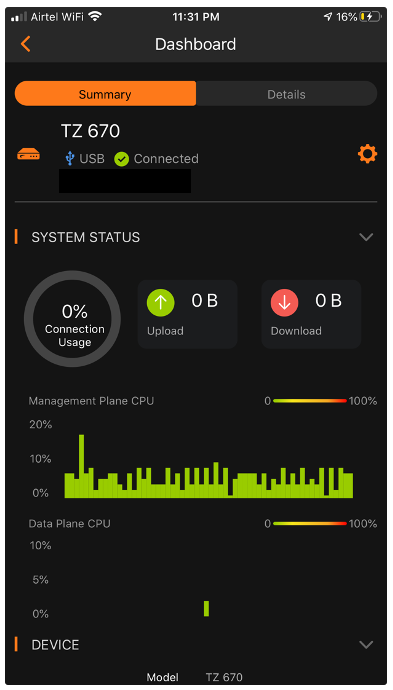
Monitoring your firewall
The SonicExpress app allows users to monitor firewalls for threat alerts, resource utilization and system status via an intuitive dashboard. It offers the flexibility of being able to check the health of your network from anywhere and the convenience of being able to make easy, quick changes necessary to ensure the security posture of your network.
There’s more coming
This is just the initial release of the app — we’ll be adding more features in future releases, including firmware management and advanced configuration capabilities similar to those available on the web management interface.
For a firsthand look at the new SonicExpress App, you can download it directly from the Apple App Store or Google Play Store.
SonicWall announces new technology
Today, SonicWall announce the following new technology that simplifies proven security for newly extended distributed enterprises, governments and MSSPs; expand breakthrough economics to high-security environments; maximize investments by delivering proven, future-proof security; and make security administration easier and more accessible to more organizations.
- New SonicOS 7.0 simplifies the security experience with an all-new user interface and experience (UI/UX), which is smartly organized, includes intelligent device dashboards, re-designed topologies, SonicExpress mobile app support, and simplified policy creation and management.
- New SonicOSX 7.0 lets governments and enterprises scale faster, protect more and maintain control. The enhanced OS simplifies complex policy, audit and management controls — all while delivering the fresh, modern and easy-to-use UI/UX available on the new SonicOS 7.0 offering.
- New SonicWall Network Security Manager (NSM) 2.0 helps organizations re-gain visibility for sprawling, mass-scale environments. Optimize, control, monitor and manage tens of thousands of network security devices, including firewalls, managed switches and access points. A cloud-native management platform, NSM is designed for speed, scalability and reliability across the largest distributed enterprises.
- New SonicWall NSsp 15700 high-end firewalls, with multiple 100/40/10 GbE interfaces, TLS 1.3 support and compute-cluster-like processing capacity, help enterprises, governments, data centers and MSSPs get more from their investments as resource utilization and connection requirements grow with the explosion of connected devices and users.
- New SonicWall TZ570 and TZ670 next-generation firewalls are the first desktop firewall form factor to offer multi-gigabit (5/10G) interfaces for connectivity with SonicWall Switches or other networking devices in SD-Branch deployments — all with more than three times the threat performance and TLS 1.3 support.
- New SonicWall NSv 270, 470 and 870 virtual firewalls simplify protection of private and public cloud assets with scalable, virtual and cost-effective security.
- New SonicWall SonicExpress allows administrations to manage security on the go. Complete the most common management tasks, including firewall registration, setup, configuration and monitoring, and easily onboard new firewalls within minutes with three easy steps: register, connect and manage.
- New SonicWall CSa 1000 stops advanced cyberattacks that target large networks via an all-new on-premise appliance. CSa includes access to RTDMITM, which provides network-based protection against the future of side-channel attacks such as Meltdown, Spectre, Foreshadow, PortSmash, Spoiler, MDS and TPM-Fail.
For the full announcement, please read the press release, explore additional details on the SonicWall blog and see the new line of NSsp firewalls, TZ firewalls, NSv firewalls, NSM 2.0 and CSa 1000. SonicWall’s commitment has always been to help protect you, your business and your brand in the new business normal. Today, it’s never been easier to realize true cybersecurity by breaking free from the constraints of the past.
Blocking HTTPS Websites, your How-To
Using the SonicOS 6.2.5.3 or earlier versions of these firewalls, we’ll take a look at how you can block unwanted HTTPS websites, the steps and procedures to follow as well as some of the advanced features to implement.
Starting at the very beginning….
In earlier versions of the HTTPS traffic filtering, IP addresses would carry out the work, and filtering would be carried out based on these IP server addresses.
When we talk about Content Filtering, this applies to all domains entered within lists you create as well as those that match these lists (Match Objects), which can all be entered in your Allowed and Forbidden lists.

These points can be found with the Firewall application pages.
Ultimately, what this means is that when you enable Filtering for HTTPS Content, the information will be scrutinised under CFS, Configure, CFS window.
This CFS setting is globally applied and relates to:
- Forbidden Domains
- Allow Domains
- CFS Allow/Forbidden List (App Rules)
- CFS Category List (App Rules)
Keyword Blocking
From here you can get hostnames in two particular ways:
1. Finding the hostname to get rating info, by examining SSL Hello. If upon examination, you discover it supports the SSL server name and extension, you will be able to find the hostname in SSL Hello Client.
2. Finding the Common Name, again, by examining the Server Hello certificate.
How to block HTTPS Content
To ensure that the content you want to block is 100% blocked, you also need to configure this for HTTPS.
To do this, you need to log in to your SonicWall management system and choose the Security Services and Content Filter tab.
From here, within the Content-Type, make sure SonicWall CFS is selected and click on Configure.
Finally, change this to Enable and to make sure all changes are saved, click OK.
Users and Zone Screens
Within the SonicWall firewall settings, you can also add the custom list for Allow or Forbidden in CFS by selecting zone and user screens through CFS Policy Assignment heading.
Once this has been changed, make sure to click accept.
Within the Content-Type, click Configure once, and only once, SonicWall CFS has been selected.
Then you can move on to the Custom tab list.
To add custom lists, click on the Add button below the Forbidden Domains box and enter the sites/apps that you would like to block.
When you’re finished, click OK to save changes.
How to configure your custom policies to include your Allow/Forbidden list
Whatever has been included within the Forbidden box automatically applies to default policies.
However, to ensure the same applies to the Custom CFS policy, this needs to be manually agreed and input.
To do this, locate the Customs CFS Policy, Edit, and click on the Settings tab.
Change the field Source to Global for Forbidden Domains and click OK.
How, using App rules, you can add Allow and Forbidden Customised Lists to CFS
Going back into Security Services and locating the Content Filtering Page, make sure to choose App Rules found in CFS Policy Assignment – then click on Accept.
To match objects…
Open up your SonicWall firewall settings and find Match Objects. Choose the option Add New.
Here you will then be able to add your customised list of forbidden and allowed websites and domain names by selecting CFS Allow or Forbid.
You also have the option of loading such lists from files containing the names of your chosen domains – however, note, each domain should be on a separate line to the previous for it to be recognised, and there is a maximum file size of 8192 bytes.
Custom List Objects differ from CFS zones and users as it can’t be used as a standalone as it will only appear with a CFS Category List.
In these instances, it’s important to set your App Rules.
To do this, you need to go into your SonicWall application control and look for the App Rules.
Here you can tick the box to Enable and choose to Add New to create your own App Rules.
All messages recorded
SonicWall firewalls are sophisticated security applications used to provide you with maximum protection.
As such, they also provide you with detailed log messages showing users when CFS has blocked HTTPS websites.
Note: Users can’t and won’t see full logs, only that the page they have requested is not permitted at this time.
To find out more about SonicWall and how we can help protect you and your users further, call us on 0333 2405667 or visit this page.
Read the next article: How your SonicWall Firewall can protect you against even the worst cyber attacks
New Features in upcoming SonicOS 7.0
SonicOS 7.0 is the upcoming unified feature release that runs on all Gen 7 firewalls. Key highlights of the upcoming SonicOS are:
- New UX/UI (Dashboard, Device information, API, Topology view, Optimized policy engine)
- Storage support
- TLS 1.3 support
- Global search for static data
- Gen7 Connections scalability (SPI, DPI, DPI SSL)
- WWAN USB card support (5G/LTE/4G/3G)
- Gen7 SonicExpress Mobile app support
- SonicWall Switch Integration support
- NSM 2.0 support (Gen7 Zero-Touch Registration and Provisioning)
Blocking pesky apps and multimedia sites using application control
ne of the most common questions we get asked is how to use the controlled features within firewall software to block pop-ups and apps such as YouTube etc.
Using SonicWall firewall software, we'll talk you through how to block a program, as well as use some of the advanced features within the operating system.
Blocking programs using SonicWall Firewall
Our step by step guide below is based on the SonicWall management system.
Firstly, you need to login to your firewall system and click on Manage displayed across the top of the bar.
Then look for Rules Advanced Application Control (in some operating systems this page can be found under Security Services.
On this page, you then need to choose and tick the box that states Enable App Control, and for these changes to be accepted, click the Accept button to enable this control feature.
Then within the App Control Advanced and category, choose Multimedia, and click Configure.
Finally, within the Edit App Category window, within the Log and Block criteria, choose to Enable for both of these.
Once complete, click, OK.
If there is a multimedia site or a specific app that you would like to block, for example, YouTube the steps to block individual apps are as follows:
Go into App Control Advanced and look for Advanced Application Control.
Within this section, you can then choose the app or multimedia site in question, i.e., YouTube.
You then need to click Configure.
Again, within the Edit App section, and under the Log and Block criteria, you need to choose the option Enable for the individual site you have selected to be blocked from your network.
To ensure all changes are saved, click OK.
SonicWall Application Control
The SonicWall firewall has several signatures covering a variety of multimedia sites and apps, providing you with the option of whether you would like these programs blocked or not.
It’s important to know how to block unwanted apps and programs on an individual level, but it is also worth noting the signatures included within SonicWALL’s App Control.
The list of most up to date signatures can be found HERE.
Local Area Networks and Application Control
In some instances, it may be applicable to enable application control if you are operating using a Local Area Network (LAN).
To do this, on the top bar, locate Manage, and scroll to Navigate to Network / Zones.
From here, you can simply click on the configure button located under the network zone that you wish to enable the App Control for.
Make sure that you tick the box labelled, Enable App Control Service (found at the bottom right of the pop-up page).
Click OK so all changes can be saved.
Does it work?
This is a good question, and if we’re honest, the only way to truly find out is to test it!
To test, we’d advise you to log in to a site or app that you have recently blocked, such as the YouTube example we mentioned above – and do this from a host behind the SonicWall.
When logging in, use either HTTP or HTTPS, so you get the message reading, `the connection was reset page`. A message will also be logged in the SonicWall, which states that the connection was reset and that ultimately the site you are trying to access is unavailable at the moment.
If you use the HTTPS route, YouTube will display on your screen; however, you won’t be able to see anything or play any videos or content, and a further error message will also be displayed on the screen.
Within your SonicWall firewall, these attempted logins will be recorded for you to see.
If you are using earlier versions of SonicWall
If you are using earlier versions of firmware and SonicOS 6.2, the steps below will allow you to block apps and sites similar to what we have mentioned above.
Firstly, you need to login to your SonicWall management and locate your firewall within the App Control Advanced tab (this page may also be named Security Services).
Make sure to tick the box named Enable App Control - click Accept for all changes to be saved.
Then, in App Control Advanced, View Style, choose within the category, Multimedia.
Click Configure and move to Edit App Category, wherein the Log and Block criteria, change these to Enable.
Finally, hit OK.
Blocking specific and individual apps and sites
Again, we’ll use the example of YouTube as the app to block. Within the App Control Advanced page, look for the View Style Application.
Here you will be able to select the individual site or app you are looking to block/restrict.
Once you have chosen the site, click configure and move to Edit App Control App, change the Log and Block criteria to Enable.
Again, make sure to click OK, so all changes are saved.
SonicWall Firewall settings are designed with users in mind, so you will find them to be straightforward and easy to manoeuvre.
If you want any further information on SonicWall, Firewalls, and how to ensure your networks are 100% protected, call us on
SonicWall launches new range of network switches
Packed with features, these stackable switches are available in a compact form factor with an energy-efficient design. Available in seven models, ranging from eight to 48, with gigabit and 10 gigabit Ethernet ports, the switches work seamlessly with SonicWall next-generation firewalls and SonicWave APs to create an end-to-end multi-gigabit secure network. The Ethernet ports provide PoE options to power on various devices such as APs, VOIP phones and IP cameras.
Learn more: https://www.sonicwall.com/resources/videos/sonicwa...
See here for a list of products.

Increased Connection Capacity on SMA 210 / SMA 410
SonicWall have released the SonicWall Secure Mobile Access firmware 10.0.0.5.
SonicWall SMA 10.0.0.5 is a maintenance release that increases maximum connection capacity and fixes issues found in previous releases. See the Enhancements and Resolved Issues sections for more information (Release Notes).
This release supports all the features and resolved issues from previous SMA 10.0 releases.
You must have an active support agreement on your SMA device in order to download and install updates. SMA appliances and subscriptions can be found here


