|
Affected SonicWall Security Appliance Platforms:
Gen5: NSA E7500, NSA E6500, NSA E5500, NSA 5000, NSA 4500, NSA 3500, NSA 2400, NSA 240, TZ 210, TZ 200, TZ 100
Firmware/Software Version: Enhanced 5.2 and above
Services: VPN using iPad/iPhone/iPod Touch (using L2TP option on the SonicWall appliance)
Feature/Application:
This document explains how to configure the iPad/iPhone/iPod Touch (we will refer to the name iPad for the rest of this document) L2TP Client access to the SonicWall WAN GroupVPN SA using the built-in L2TP Server. This guide is for SonicOS Enhanced 5.2.x firmware.
Procedure: iPad Configuration
Follow these steps to configure the iPad to connect to the SonicWall GroupVPN SA using the built in L2TP Server.
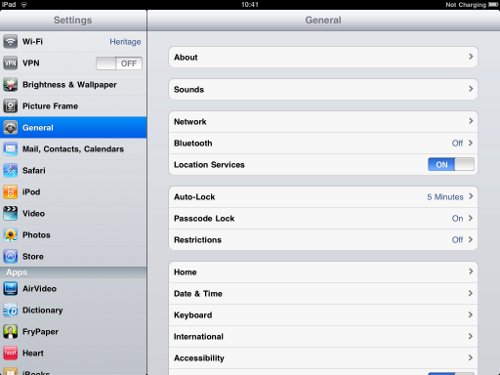
Step 1: From the Home Screen, press the Settings icon

Step 2: Next, from the General menu, select Network
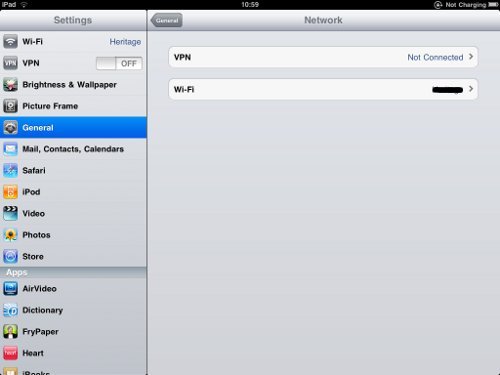
Step 3: In the Network menu, select the VPN option
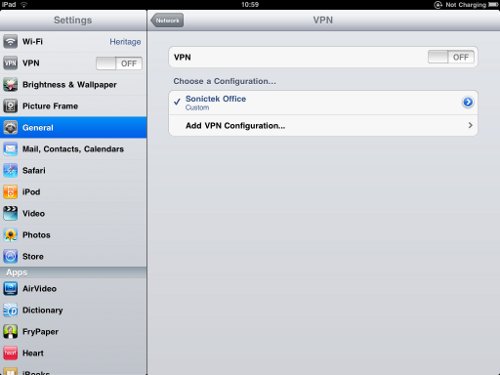
Step 4: In the VPN menu, choose the heading titled, Add VPN Configuration
Step 5: In the Add Configuration menu, make sure L2TP is selected

Step 6: Fill out the Required fields, then press save when you are done
- Description: This is a friendly name for your VPN configuration
- Server: This is the WAN IP (or host name) address of your SonicWall
- Account: This is the user account created for accessing the network via VPN; because we use LDAP (AD integration) on our firewall we have to use local users to authentication this VPN because the iPad uses CHAP authentication and isn't compatible with LDAP, although you could change to Radius instead if you want to use external users/passwords.
- RSA SecurID: Not used in this configuration
- Password: If left blank, every time a connection is established, a prompt for your password will appear. If completed, then the iPad will store your password for future connections
- Secret: This is your pre-shared secret configured within the WAN GroupVPN policy
- Send All Traffic: This will allow for either split tunnel or route-all depending on VPN configuration. This example will use the route-all config (we prefer to allow internet traffic locally by the user rather than force down the tunnel )

Step 7: The saved configuration will appear on the VPN screen. You can then slide the VPN to the ON position, and your iPad will begin IPSec communication

|